ITS Blog: News in Post-Quantum Cryptography – April 2026
4 min
Welcome to another regular overview of key developments in the world of post-quantum cryptography (PQC). The rapid pace at which we are approaching the practical limits of quantum computers and advancements in artificial intelligence is forcing technology leaders and researchers to constantly innovate. Over the past month and a half, we have witnessed not only significant progress in hardware and software implementations of approved standards, but also alarming findings regarding vulnerabilities in current encryption.
Here is a summary of the most important points that no IT strategist or security architect should overlook.
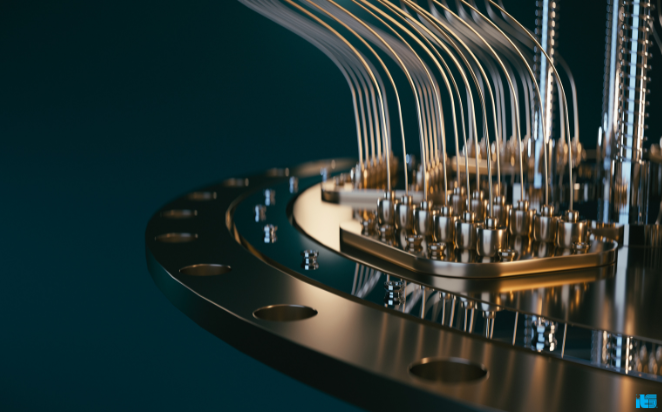
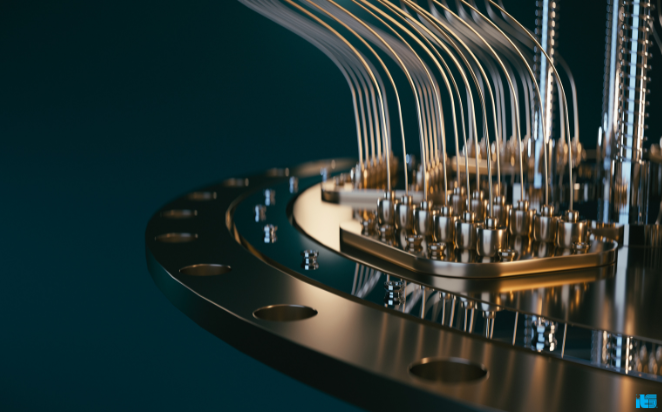
Industrial Implementations and Hardware Security
Microsoft is fully integrating PQC into Windows – Microsoft has released a comprehensive guide the transition to PQC and announced the integration of quantum-resistant algorithms (ML-KEM per FIPS 203 and ML-DSA per FIPS 204) directly into its native SymCrypt cryptographic library. Additionally, support for hybrid TLS key exchange at the Schannel stack level has been released as part of the Windows Insider program for Windows Server 2025 and Windows 11. This is a crucial step toward building so-called crypto-agility for enterprise customers.
SEALSQ integrates PQC directly into silicon – the hardware technology company SEALSQ has unveiled the integration of PQC algorithms directly at the chip level (hardware microcontrollers). This shift of protection to the physical layer (Hardware Root of Trust) aims to defend enterprise infrastructure against unauthorized tampering and increasingly sophisticated AI tools capable of quickly identifying vulnerabilities at the software level.
Standardization and Legislation
ENISA Addresses Quantum-Secure Digital Identity – ENISA has launched a public consultation on a proposal for a new certification scheme for the EU Digital Wallet. The new proposal directly addresses the protection of sensitive data and cloud services against quantum threats using PQC standards.
Pressure on critical infrastructure is mounting: as spring draws to a close, Western regulatory bodies (including CISA and the EU’s NIS2 Directive) have begun formally urging critical infrastructure operators to move from preparation directly to implementation. According to the latest recommendations, critical infrastructure operators and cloud providers must begin migration processes by the end of 2026, including the introduction of regular progress reports (as required, for example, by the new Canadian model starting in April).
Research, Threats, and Implementation Risks
Google Dramatically Lowers Estimate for ECC Break. Google Quantum AI’s research team has published a groundbreaking cryptanalytic report that reduces the estimated number of qubits needed to break elliptic curve cryptography (ECC) by as much as twentyfold. This discovery significantly moves the consensus “Q-Day” (the day today’s ciphers are broken) much closer to the present and changes quantum risk assessment models in both the commercial and financial sectors.
Artificial intelligence streamlines the collection of encrypted data and shortens the lifespan of traditional cryptography. Anthropic has unveiled an AI model called “Claude Mythos Preview,” which, according to security experts, demonstrates unexpectedly strong capabilities in automatically detecting long-standing and complex software and cryptographic flaws. This level of intelligence changes the dynamics of attacks in two fundamental ways. First, it drastically streamlines the “Harvest” phase (data collection) itself—AI enables attackers to discover vulnerabilities (so-called zero-days) more easily and quickly and to massively download and stockpile encrypted data from third parties. Second, by uncovering hidden mathematical weaknesses in current ciphers, it shifts the threat from a long-term “Decrypt Later” scenario to a much more immediate “Decrypt Sooner” scenario.
It is therefore unlikely that the collected data will need to be "cracked" a decade from now using a full-fledged quantum computer; instead, this will be achieved much sooner thanks to advanced cryptanalysis driven by artificial intelligence.
You can surely draw your own conclusions from the events of recent weeks. It is more than obvious that the issue of post-quantum threats is increasingly coming to the forefront and sparking new discussions on security.
Text: František Kovařík, ITS
What else to read
See more news from the world of IT and ITS